In week 48, the IP addresses responsible for most of the malicious network activity on TEHTRIS honeypots are recorded in the United-States (19,42%), in Netherlands (15,44%), in United-Kingdom (11,68%), in Bulgaria (7,96%), in China (7,43%) et in Russia (6,06%).
This week, TEHTRIS is referring to 3 malicious activities observed on its international honeypot network.
Persisting attempts to compromise by default credentials on SSH
By default credentials: nproc/nproc
This week, nearly 20% attempts to compromise SSH correspond to using credentials nproc/nproc on all our European honeypots. These by default credentials have been tested by almost 3 500 unique IP addresses. The combination of the “nproc” login with the “nproc” password are the credentials used on devices run with Linux. The command nproc is used to count the number of available processing units available. This command can be used for system diagnosis. It is part of the GNU Core utilities and is available on all modern Linux operating systems.
By default credentials: 3comcso/RIP000
To access to your 3Com SUPERSTACK II router, you need to connect to the IP of the device and enter the associated credentials given. But it is also possible to use by default credentials that are the login “3comcso” and the password “RIP000”.
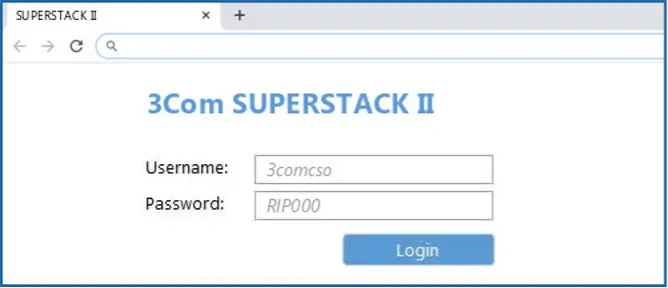
The cyber threat actors only have to test a large number of IP addresses with those by default credentials in an automatic way to find compromised routers.
This week, these by default credentials have been tested by 6 unique IP addresses on our European honeypots, mostly targeting Polish, German, and Belgian infrastructures, as well as Czech, Italian, French, Finnish, Dutch, British and Lithuanian.
IoCs :
| IP | % | AS | Country |
| 195.3.147[.]57 | 50.225% | AS 41390 RN Data SIA | LV |
| 193.105.134[.]95 | 45.27% | AS 42237 w1n ltd | SE |
| 45.141.84[.]126 | 3.153% | AS 206728 Media Land LLC | RU |
| 45.141.84[.]10 | 0.676% | AS 206728 Media Land LLC | RU |
| 185.217.1[.]246 | 0.45% | AS 42237 w1n ltd | SE |
| 31.184.198[.]71 | 0.225% | AS 34665 Petersburg Internet Network ltd. | RU |
The Russian IP address 45.141.84[.]126 is identified as belonging to the cyber gang Karakurt since August 2022.
Using automatic methods allow the cyber criminals to attempt to get access using by default credentials targeting the whole Internet.
TEHTRIS recommends modifying by default credentials of all your connected devices, and more broadly, to respect good digital hygiene rules, in order to avoid falling in the trap of automatic tools created by threat actors.
New attempts of bruteforce on SMB protocol
This week, more than 30% of IP addresses that performed bruteforce attempts on SMB protocol on TEHTRIS honeypots are unknown from public data bases. 5 among them are located in South America.
IoCs :
| IP | AS | Country |
| 152.231.117[.]27 | AS 27651 ENTEL CHILE S.A. | CL |
| 186.122.247[.]214 | AS 11664 Techtel LMDS Comunicaciones Interactivas S.A. | PY |
| 96.10.242[.]118 | AS 11426 TWC-11426-CAROLINAS | US |
| 220.133.4[.]234 | AS 3462 Data Communication Business Group | TW |
| 186.10.109[.]195 | AS 27651 ENTEL CHILE S.A. | CL |
| 187.169.25[.]126 | AS 8151 Uninet S.A. de C.V. | MX |
| 201.243.229[.]91 | AS 8048 CANTV Servicios, Venezuela | VE |
Beware of vulnerabilities’ automatic scans
This week, 208 scan attempts on our European honeypots have been performed thanks to the following url request:
GET /w00tw00t.at.ISC.SANS.DFind:)If you spot this log in your infrastructures, it means that a scan is ongoing on your website and/or server, either on the occasion of an official audit, or because it is performed by a cyber threat actor, using vulnerability scanner tools such as Dfind port scanner.
3 unique IP addresses have requested this url. Here are the IoCs:
- 167.114.137[.]244 – AS 16276 OVH SAS – CA
- 178.238.238[.]29 – AS 51167 Contabo GmbH – DE
- 198.50.176[.]11 – AS 16276 OVH SAS – CA
To be noticed, in public data bases, the firt IP address is associated with the Grandoreiro banking trojan by Zscaler since August 2022. According to their study, this campaign is targeting organizations in the Spanish-speaking nations of Mexico and Spain that work across a variety of different industry verticals such as Automotive, Chemicals Manufacturing and others.
These large-scale scans launched by cyber threat actors enable them to find targets vulnerable to their malware, or to find out their target’s vulnerabilities in order to create the appropriate malware.
TEHTRIS recommends protecting your website and/or server from potential outside scan because such software can reveal many sensitive information regarding technical flaws of the tools you use on a daily basis. The TEHTRIS EDR solution, unified with complementary modules inside the XDR Platform, has an Audit module that identifies all vulnerabilities on endpoints including servers.